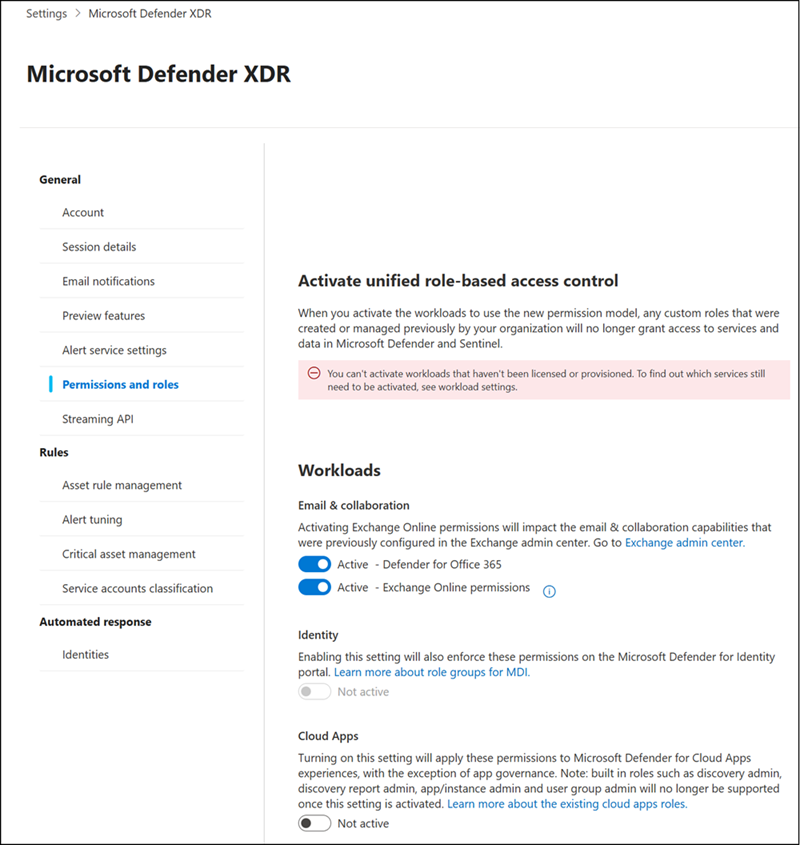
Microsoft Defender for Office 365 is aligning permissions management with the Defender XDR Unified role-based access control (Unified RBAC) model.
Starting at the end of May 2026, all newly created tenants with Defender for Office 365 Plan 2 will use Unified RBAC by default.
Timeline
The rollout is scheduled for 30 May to mid-June 2026.
How does this affect your organization?
Microsoft will enable Unified RBAC by default for all newly created tenants on or after 30 May 2026 if the tenant includes a Defender for Office 365 Plan 2 license or service plan, such as when you start a 30-day trial of Office 365 E5. Existing tenants keep their current permission model with no changes required.
This change may be relevant for users with the Security Administrator role who still use the older Microsoft Defender XDR roles in existing tenants. Security administrators can use Unified RBAC roles together with Microsoft Entra roles to manage access in the Microsoft Defender portal, with Unified RBAC as the recommended option.
Unified RBAC is already enabled by default if a new tenant includes the following products:
- Tenants created on 16 February 2025 or later with Defender for Endpoint
- Tenants created on 2 March 2025 or later with Defender for Identity
- NEW: Tenants created on 30 May 2026 or later with Defender for Office 365 Plan 2
What is the difference between the Unified RBAC model and the roles in Microsoft Defender XDR?
Microsoft Defender XDR Unified RBAC is the modern, centralized role-based access control system built into the Microsoft Defender portal. It lets you define granular permissions across all Defender workloads (Defender for Endpoint, Defender for Office 365, Defender for Identity, etc.) from a single place. You build custom roles by combining specific permission sets, which apply across the integrated Defender services. Unified RBAC replaces the older, workload-specific permission models and gives you fine-grained control over what users can see and do.
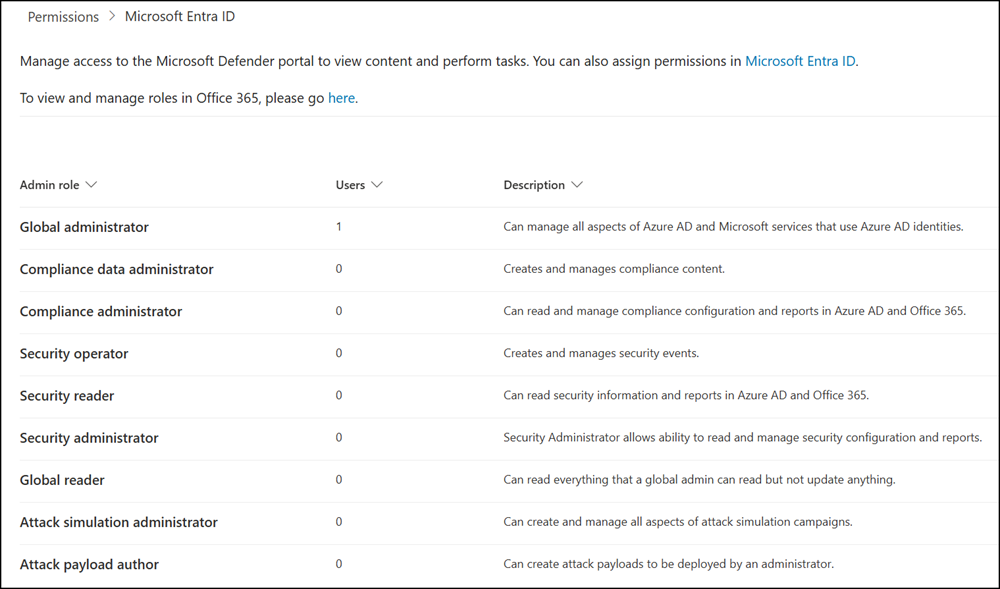
Microsoft Defender XDR roles refer to the older, simpler model that maps to Microsoft Entra built-in roles, primarily Global Administrator, Security Administrator, Security Operator, Security Reader, and others. These are coarser-grained and not specific to Defender workloads. When Unified RBAC is not activated for a workload, Defender falls back to these Entra roles to determine access.