As published last October, Microsoft has updated the Revoke multifactor authentication sessions action in Microsoft Entra.
Previously, this action applied only to the legacy per-user MFA enforcement, not to the recommended MFA configuration via Conditional Access.
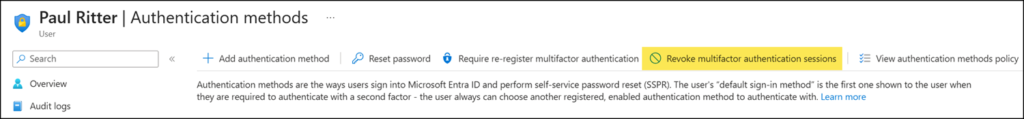
The updated “Revoke sessions” action invalidates all user sessions, including MFA, regardless of whether MFA is enforced via Conditional Access or per-user policies. This action triggers revokeSignInSessions via Microsoft Graph.
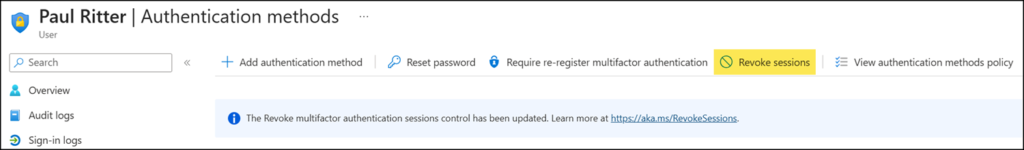
Confirming the action.

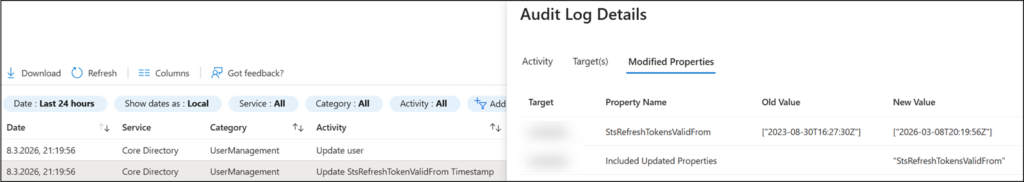
The action resets signInSessionsValidFromDateTime and is logged under the audit activity Update StsRefreshTokenValidFrom Timestamp.
The affected account will be required to re-authenticate on all connected devices.
Session revocation can also be directly triggered via Microsoft Graph.
As Microsoft documents, the remediation steps are to disable the account, revoke the session, and disable the associated devices.
Import-Module Microsoft.Graph.Authentication
Connect-MgGraph -Scopes "User.ReadWrite", "Directory.AccessAsUser.All"
$UPN = "<UserPrincipalName>"
$UserObject = Invoke-MgGraphRequest -Method GET -Uri "https://graph.microsoft.com/v1.0/users/$UPN"
# Disable the account
$Body = '{ "accountEnabled": false }'
$Url = "https://graph.microsoft.com/v1.0/users/$($UserObject.id)"
Invoke-MgGraphRequest -Method PATCH -Uri $Url -Body $Body -ContentType "application/json"
# Revoke all refresh tokens
$Url = "https://graph.microsoft.com/v1.0/users/$($UserObject.id)/revokeSignInSessions"
Invoke-MgGraphRequest -Method POST -Uri $Url
# Disable all registered devices
$Url = "https://graph.microsoft.com/v1.0/users/$($UserObject.id)/registeredDevices"
$UserDevices = Invoke-MgGraphRequest -Method GET -Uri $Url
foreach ($Device in $UserDevices.value) {
$Body = '{ "accountEnabled": false }'
$Url = "https://graph.microsoft.com/v1.0/devices/$($Device.id)"
Invoke-MgGraphRequest -Method PATCH -Uri $Url -Body $Body -ContentType "application/json"
}
